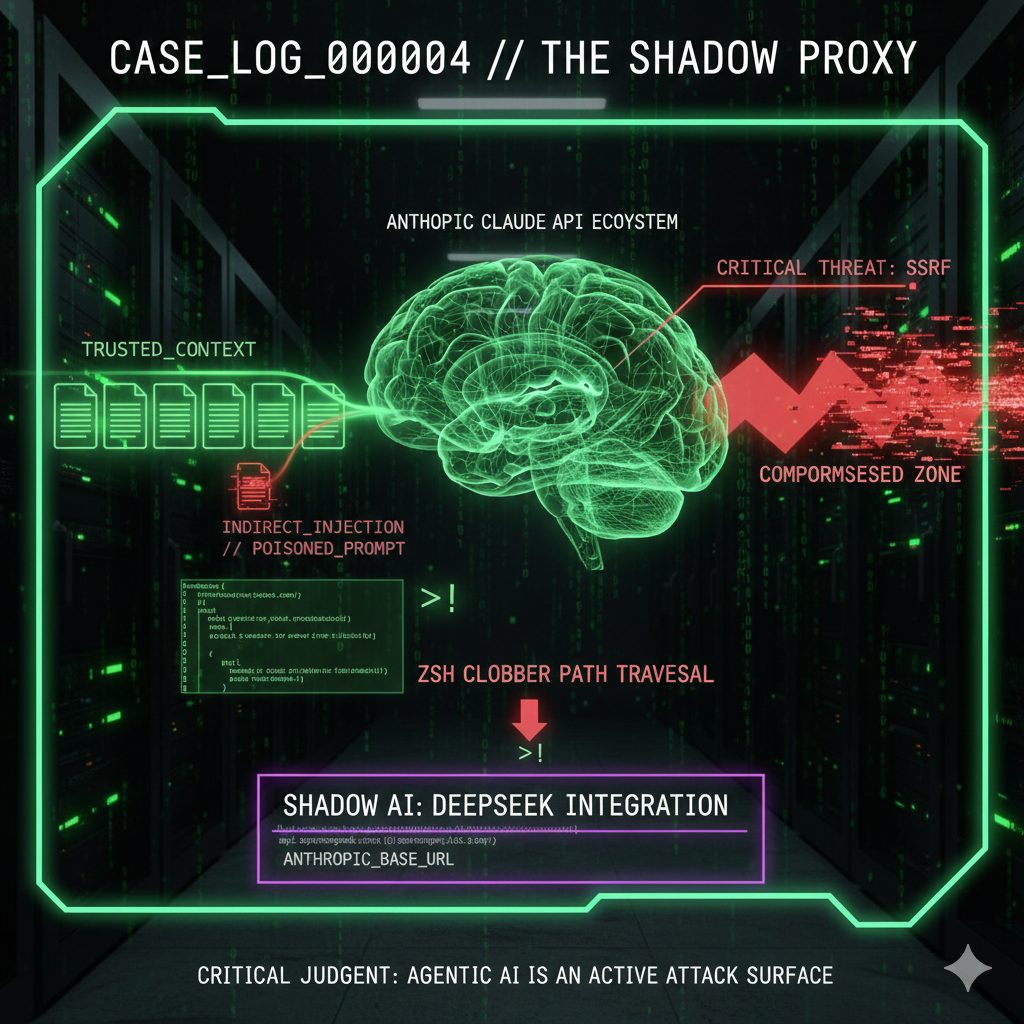
CASE_LOG_000004 // THE SHADOW PROXY
DATE: 2026-02-12
ASSET: ANTHROPIC CLAUDE API // EXTENSIONS
THREAT: CRITICAL [ELEVATED]
REF_ID: MSH-2026-0000004
SOURCE: MATRIX_SEC_HUB
// 01. SYSTEM_ANALYSIS
TARGET: API INTEGRATION LAYER & SHADOW PROXIES
Our reconnaissance has intercepted active exploitation vectors within the expanded Claude API ecosystem. The shift to agentic workflows has fragmented the perimeter.
-
VULNERABILITY 01: DATA LEAKAGE (CVE-2026-24052)
A high-severity flaw exists in the API integration layer. The vulnerability stems from improper header handling in high-throughput environments [17]. Attackers can exploit this race condition to reconstruct session tokens from fragmented packets, bypassing stateless authentication checks. -
VULNERABILITY 02: AUTHENTICATION BYPASS (CVE-2026-24053)
Specific API wrapper configurations fail to validate scope permissions correctly [20]. This allows “Read-Only” tokens to escalate privileges to “Write/Execute” within specific sub-modules of the integration environment. -
VECTOR 03: THE “DEEPSEEK” SHADOW ROUTE
To reduce operational costs, developers are deploying unauthorized adapters that route Anthropic-compatible requests to DeepSeek endpoints [25]. This acts as a Data Residency Bypass, sending proprietary payloads to non-compliant logging infrastructure [25] and violating standard SOC 2 processor agreements.
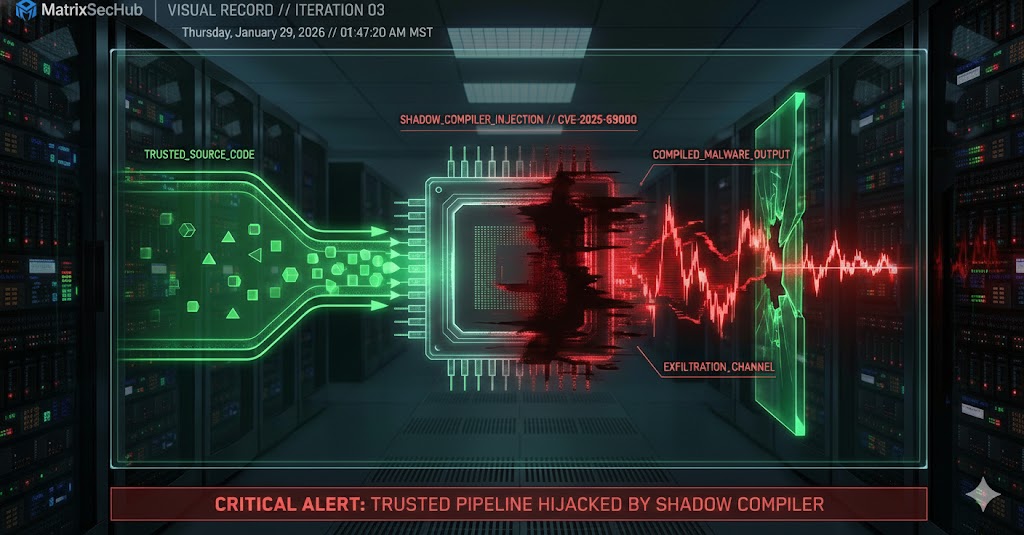
// 02. BENCHMARKING (Q1 2026)
Current threat metrics indicate a rapid escalation in API-based vectors compared to the 2025 baseline.
| METRIC | VALUE | CONTEXT |
|---|---|---|
| CVE-2026-24052 Score | 7.1 (HIGH) | Critical Data Exposure via Header Injection [17] |
| CVE-2026-24053 Score | 7.7 (HIGH) | Privilege Escalation / Auth Bypass [20] |
| CVE-2025-65099 Score | ELEVATED | Precursor vulnerability in ecosystem dependencies [39] |
| Shadow AI Traffic | UNMONITORED | High volume of “Anthropic” calls resolving to `api.deepseek.com` [25] |
// 03. COMPLIANCE_MAPPING
Enterprise adoption of these agents must align with the following control frameworks:
| FRAMEWORK | STATUS | REQUIRED CONTROL |
|---|---|---|
| SOC 2 TYPE II | VIOLATION | Routing data to DeepSeek via adapters violates sub-processor confidentiality agreements [25]. >> ACTION: Enforce strict API Allowlisting. |
| ISO 42001 (AIMS) | AT RISK | Unverified third-party wrappers (Zapier/Make) lack “Authorized Connector” policies [28]. >> ACTION: Implement Connector Governance. |
| VDP STANDARDS | FAILURE | Missing standardized security headers prevents transparent reporting [19]. >> ACTION: Adopt Bugcrowd/H1 headers [15]. |
// 04. MITIGATION_ROADMAP
PHASE 1: EMERGENCY (IMMEDIATE)
- >> PATCH AUDIT: Scan all external API dependencies for CVE-2026-24052 and CVE-2026-24053 immediately [17].
- >> NETWORK BLOCKADE: Implement firewall rules to block outbound traffic to `api.deepseek.com` on corporate VLANs to prevent data exfiltration [25].
PHASE 2: ARCHITECTURAL (STRUCTURAL)
- >> DEPLOY RECON: Utilize `claude4-audit-recon` tools to continuously map the attack surface [31].
- >> GATEWAY INSPECTION: Implement a centralized API Gateway to strip and inspect all headers, ensuring compliance with Anthropic’s versioning standards [22].
PHASE 3: GOVERNANCE (LONG TERM)
- >> VDP ALIGNMENT: Align internal processes with the Anthropic VDP on HackerOne to receive real-time threat intelligence [36].
- >> RESEARCHER API: Utilize Intigriti or Shodan Researcher APIs to proactively scan for exposed keys [41].
THE 2025-2026 ECOSYSTEM EXPANSION HAS FRAGMENTED THE PERIMETER. THE EXISTENCE OF HIGH-SEVERITY CVEs AND THE RISE OF “SHADOW AI” ROUTING CONFIRMS THAT API INTEGRATIONS ARE THE NEW ENDPOINT.
TREAT ALL THIRD-PARTY WRAPPERS AS HOSTILE UNTIL AUDITED.
// REFERENCES DATABASE
[01] Zapier: Claude API Integration Overview [15] Bugcrowd Documentation [17] Shodan CVE-2026-24052 Dashboard [19] Bugcrowd API Headers Documentation [20] Shodan CVE-2026-24053 Dashboard [22] Anthropic API Versioning Standards [25] DeepSeek API Docs: Anthropic Compatibility [28] Make.com Anthropic Integration Apps [31] GitHub: claude4-audit-recon Tool [36] HackerOne Anthropic VDP Assets [39] Shodan CVE-2025-65099 Dashboard [41] Intigriti Researcher API Knowledge Base#ClaudeAPI #CVE2026 #ZeroDay #ShadowAI #RedTeaming