[ DATE: 12.25.2025 ]
[ CLASSIFICATION: EXECUTIVE BRIEFING // DEEP DIVE ]
THE ASYMMETRY OF RISK: WHY “ONE PILL” SECURITY IS A FATAL ERROR
In the architecture of modern risk, there is a glitch. It is a fundamental disconnect between how we measure security and how we experience it.
Founders are presented with a binary choice, a “False Dichotomy” that splits their defense into two incomplete realities. We call these the Blue Pill (The Compliance Illusion) and the Red Pill (The Operational Reality).
To understand why the modern enterprise is fragile, we must deconstruct why these two pills, when taken alone, are poisonous to your valuation.
🔵 THE BLUE PILL: THE THEATER OF COMPLIANCE
The Blue Pill is the domain of the Digital Architect. It is a world governed by frameworks: SOC 2 Type II, ISO 27001, and NIST 800-53. It is clean, linear, and binary.
THE MECHANISM:
The Blue Pill operates on the logic of “Security Theater.” It optimizes for the audit, not the adversary. It prioritizes the evidence of a control over the efficacy of a control.
- The Artifact: A clean penetration test report (often scoped to exclude physical vectors).
- The Metric: “100% Compliance” on a Vanta or Drata dashboard.
- The Value: It satisfies the Board, creates a paper trail for liability, and unlocks Enterprise sales channels.
THE FATAL FLAW:
The Blue Pill assumes a “Spherical Cow”—a frictionless environment where code is law. It forgets that Entropy exists. It ignores the janitor propping open a side door. It ignores the “Shadow IT” server under a developer’s desk. It ignores the human element entirely.
“A firewall cannot stop a man with a badge he found in the parking lot.”
🔴 THE RED PILL: THE BURDEN OF REALITY
The Red Pill is the domain of the Tactical Operator. It is the world of “Assume Breach.” It is the messy, mud-stained reality of physical access control, social engineering, and hardware hardening.
THE MECHANISM:
The Red Pill operates on the logic of “Adversarial Truth.” It doesn’t care what the policy says; it cares what the attacker does.
- The Artifact: A Faraday bag for executive travel. A “Tailgating” sensor at the lobby turnstile.
- The Metric: “Mean Time to Detect” (MTTD) a physical breach.
- The Value: It prevents the catastrophic “Black Swan” event that digital tools cannot see.
THE FATAL FLAW:
The Red Pill has a Translation Problem. In a boardroom, “Physical Security” sounds like overhead. It sounds like guards and gates, not Intellectual Property protection. Because the Operator cannot speak the language of “Risk Valuation,” their warnings are dismissed as paranoia until it is too late.
THE SYNTHESIS: THE THIRD PATH
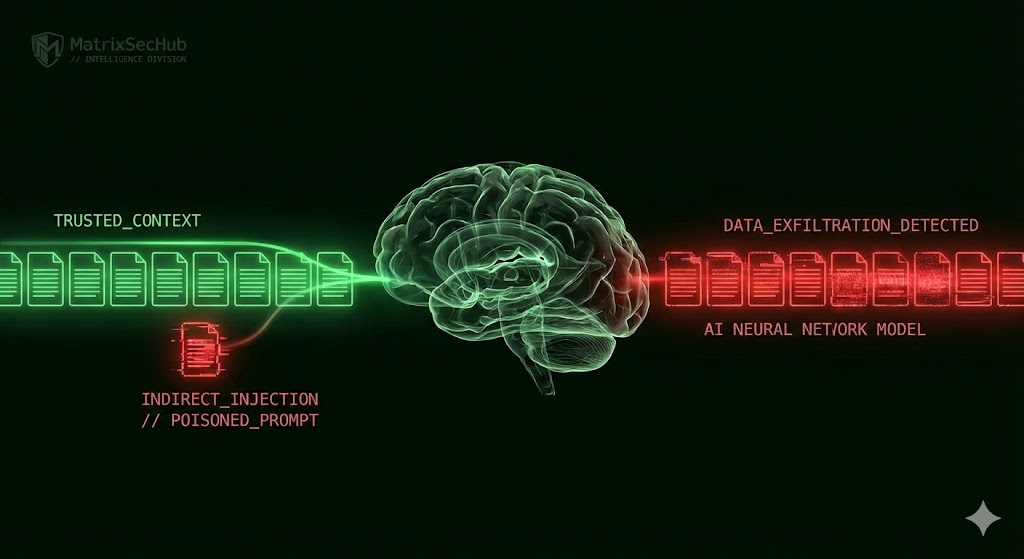
The era of the “Single Pill” is over. The modern threat landscape is Converged. A physical action (stealing a laptop) leads to a digital result (ransomware injection). A digital action (cloning a badge signal) leads to a physical result (server room access).
If your methodology forces you to choose between the Audit (Blue) and the Reality (Red), you have already lost. The adversary does not respect your silos.
The most antifragile organizations are those that ingest the tactical grit of the Operator and refine it into the systemic elegance of the Architect.
You don’t need to choose. You need to build both.
// END TRANSMISSION //
// SIGNATURE: OPERATOR_HSX //