[ CLASSIFIED_INTEL ]
CASE_LOG_045 // SILENT_KRAKEN_BREACH
DATE: 2026-02-27
ASSET: LLM INFERENCE PIPELINES & GPU CLUSTERS
THREAT: [ CRITICAL // NATION-STATE & RANSOMWARE SYNDICATE ]
// 01. SYSTEM_ANALYSIS
Adversaries utilized CVE-2025-1974 (Ingress-NGINX) and CVE-2026-21962 (Oracle Auth Bypass) to penetrate the AI perimeter. Once established, they weaponized ShadowMQ vulnerabilities to execute remote code directly on Meta Llama and NVIDIA TensorRT-LLM frameworks. Traditional IAM completely failed to prevent lateral movement from the Model Registry to the Data Lake.
// 02. BENCHMARKING (DLP EVASION)
- FGT1567.002 Exfiltration Detection: 0.0% (BYPASSED)
- Layer-7 Micro-Perimeter Efficacy: 0.0% (Not Configured)
// 03. COMPLIANCE_MAPPING
| FRAMEWORK | THE GAP | STATUS |
|---|---|---|
| Zero Trust Architecture (DoD/NIST) | Lack of service mesh mTLS across k8s GPU pods. | FAILED |
| SOC 2 (Security) | Unmonitored cloud-browser hybrid channels permitted data exfiltration. | FAILED |
// 04. MITIGATION ROADMAP
- >> 1. EMERGENCY: Patch k8s Ingress-NGINX and Oracle Fusion components immediately. Revoke over-permissioned tokens in the Model Registry.
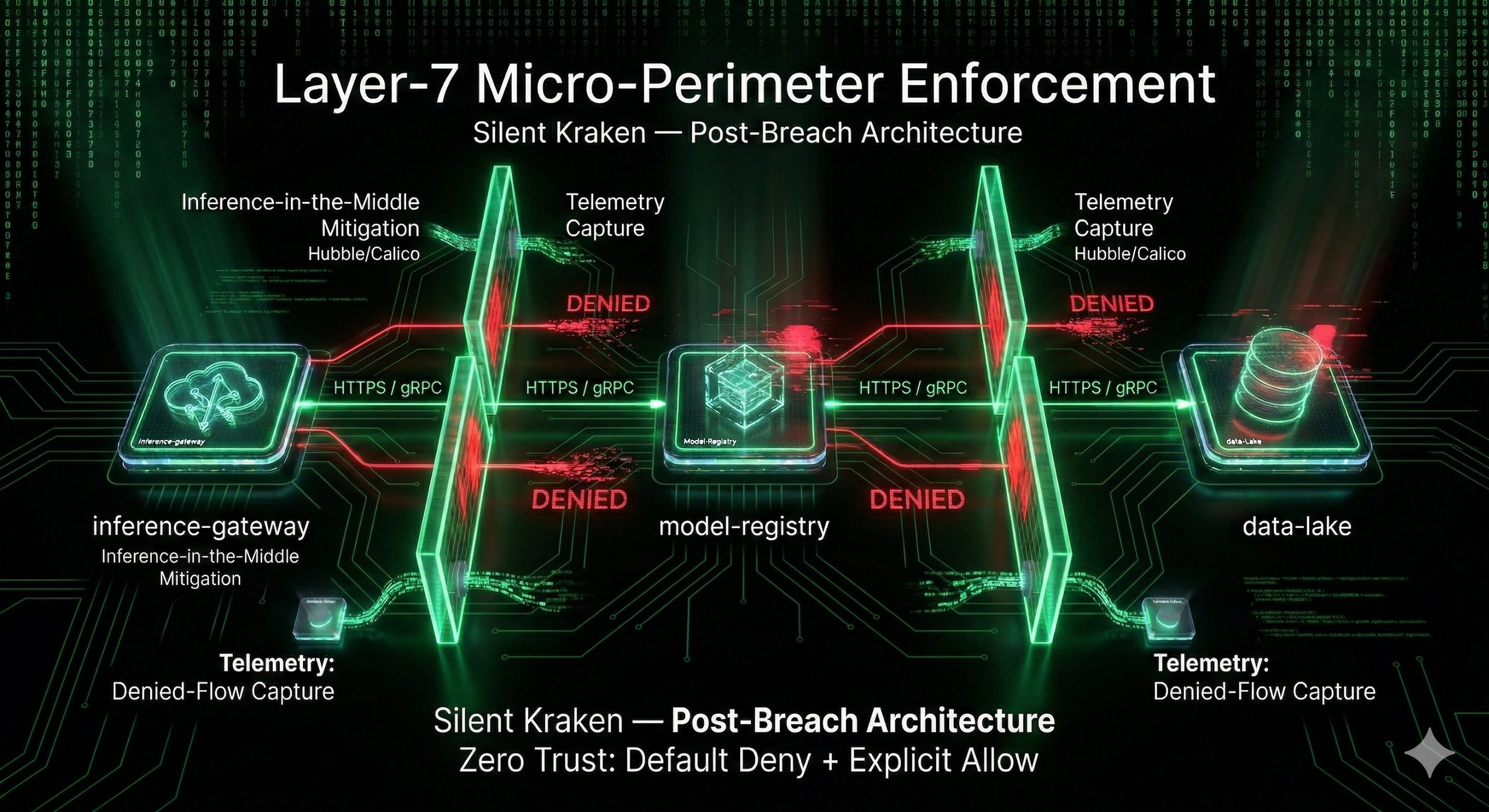
- >> 2. ARCHITECTURAL: Deploy Linkerd or an equivalent Zero Trust service mesh to enforce identity and strict Layer-7 micro-perimeters between the data lake and inference engines.
- >> 3. GOVERNANCE: Re-calibrate DLP rulesets to detect high-frequency, low-volume FGT1567.002 telemetry anomalies.
[1] CVE-2025-1974 Ingress-Nightmare Breakdown
[2] CVE-2026-21962 Oracle Fusion Authentication Bypass
[3] ShadowMQ Critical AI Flaws (Remote Code Execution)
[4] Sovereign AI Post-Mortem 2026
// MATRIXSECHUB INTELLIGENCE DIVISION // OPERATOR_SYNTHESIS_KERNEL