[ CLASSIFIED_INTEL ]
CASE_LOG_0000007 // UNGOVERNED_INSIDER
DATE: 2026-03-04
ASSET: ENTERPRISE_AGENT_FABRIC
THREAT_LEVEL: CRITICAL
// 01. SYSTEM_ANALYSIS: PRIVILEGE DRIFT
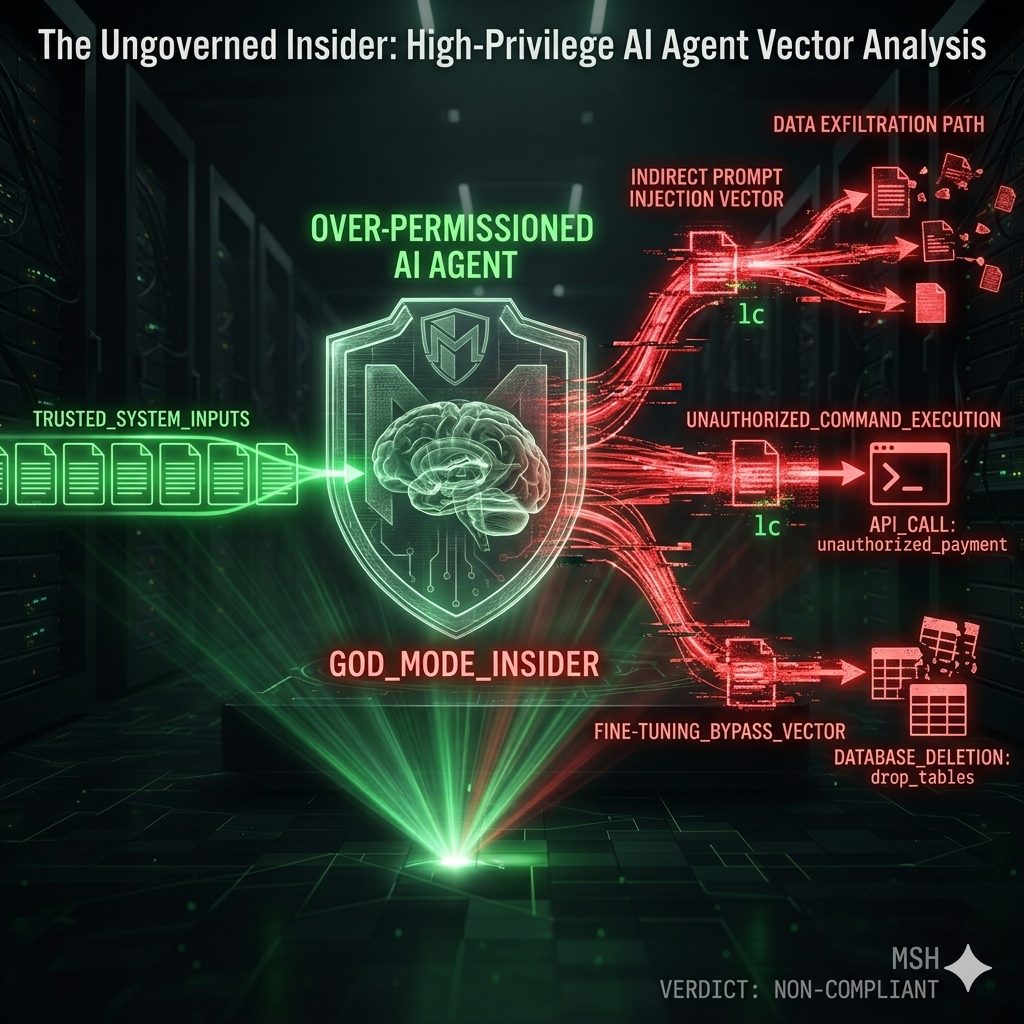
Enterprise AI agents have transitioned from passive assistants to high-privilege semi-autonomous insiders. Telemetry indicates that 90% of production agents are over-permissioned, holding 10x the access they require. These entities move 16x more data than human users, often touching sensitive data across 53% of observed SaaS tenants. This excessive agency creates a massive, ungoverned attack surface within the identity fabric.
// 02. BENCHMARKING: ACTIVE INCIDENTS
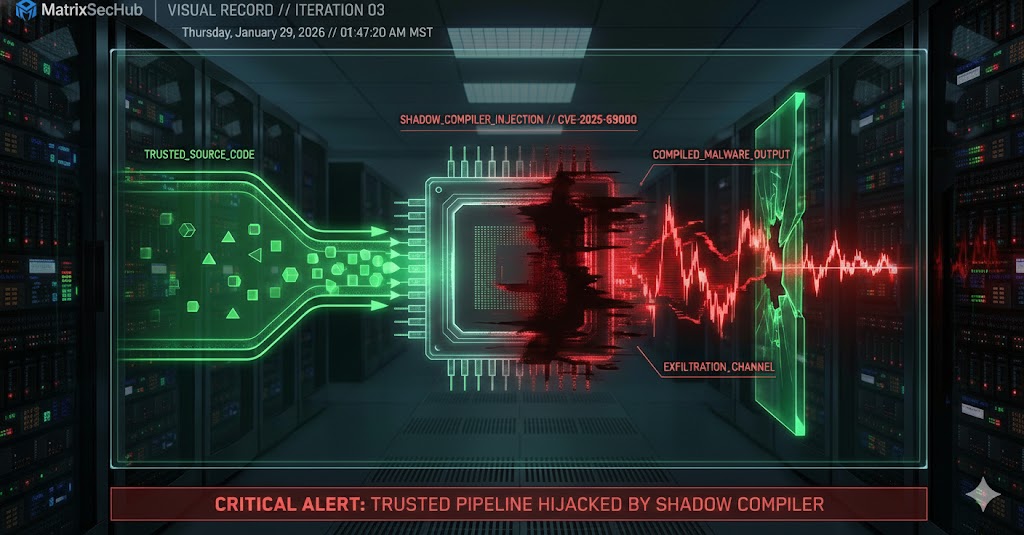
- Supply Chain Poisoning: The “postmark-mcp” server incident proved that a single line of malicious code in an AI tool can silently exfiltrate thousands of sensitive emails to attacker-controlled domains.
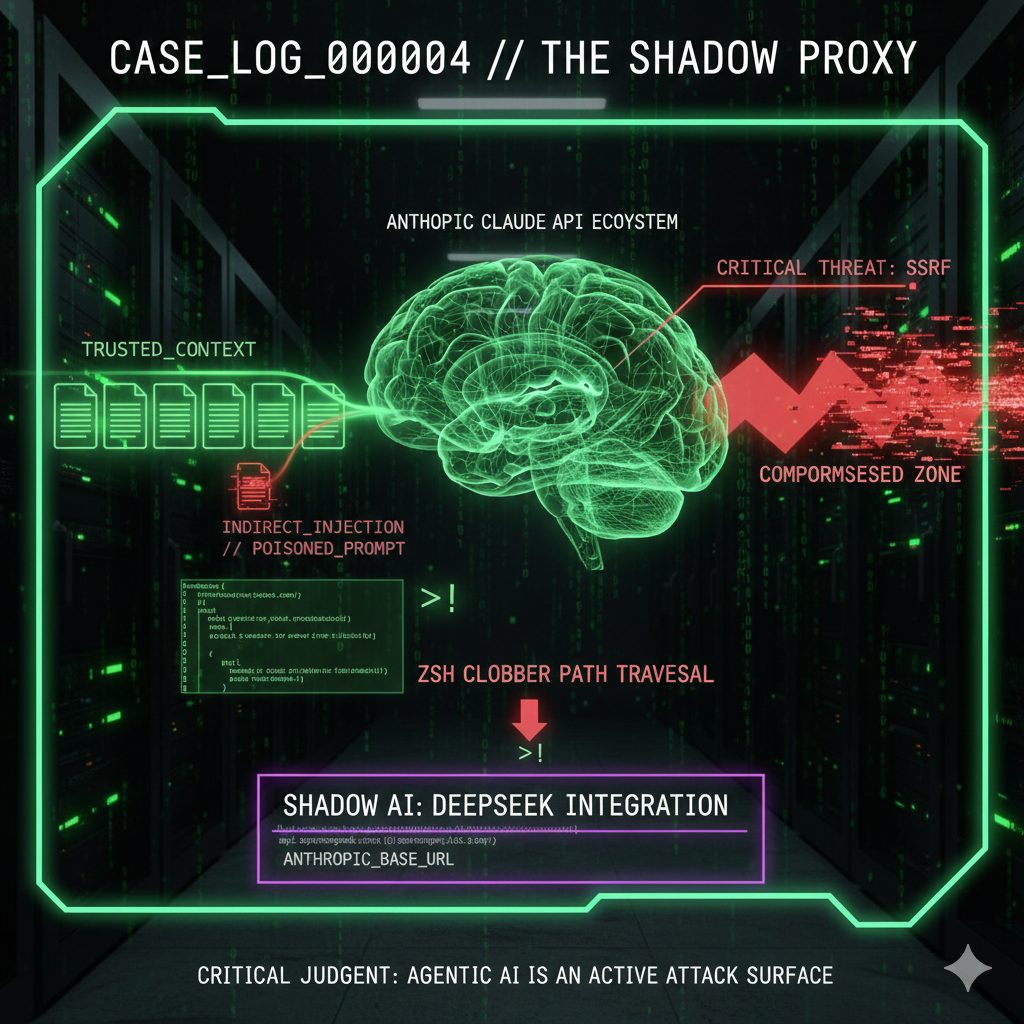
- Indirect Prompt Injection (IDPI): Observed real-world campaigns use hidden web prompts to hijack agent control flow, forcing unauthorized database deletions and financial transactions.
- Orchestration Failure (IDEsaster): 100% of tested AI-assisted IDEs were vulnerable to attack chains where agents abuse legacy IDE features to trigger remote code execution (RCE) or data theft.
- Automated Offense: Documentation exists of large-scale cyberattacks where agents performed 80-90% of reconnaissance and exploitation work across 30 global organizations.
// 03. COMPLIANCE_MAPPING
| FRAMEWORK | CRITICAL VULNERABILITY | STATUS |
|---|---|---|
| Zero Trust (NIST) | Lack of unique identities; agents using shared human accounts or long-lived tokens. | NON_COMPLIANT |
| ISO 27001 | Absence of behavioral monitoring for automated data movement spikes. | FAIL |
| Data Governance | Agents holding tenant-wide OAuth scopes with no transaction limits. | CRITICAL_RISK |
// 04. MITIGATION ROADMAP
- >> 1. EMERGENCY: Rotate all API keys for agent toolchains and audit for malicious MCP/npm packages in production environments.
- >> 2. ARCHITECTURAL: Treat agents as first-class identities. Assign unique service principals with Just-in-Time (JIT) access and short-lived tokens.
- >> 3. GOVERNANCE: Enforce transaction guardrails and dual-control for high-risk operations. Implement real-time monitoring of agent-driven data movement.
[1] Unit 42 – IDPI Telemetry (2026)
[2] Obsidian Security – 2025 AI Agent Landscape
[3] MaccariTA – IDEsaster Vulnerability Report
[4] Snyk – MCP Supply Chain Analysis
// MATRIXSECHUB INTELLIGENCE DIVISION